Shodan search for VNC open access: How to find VNC service without authentication with help of Shodan search engine.
Previously we learned what is Shodan and how does it works. Now let’s try to understand how we can find hosts with open VNC service with help of the Shodan search engine.
About VNC
First need to understand what is VNC and why do we need to search it.
VNC – Virtual Network Computing, graphical desktop sharing system that uses the Remote Frame Buffer protocol to remotely control another computer.
It transmits the keyboard and mouse events from one computer to another, relaying the graphical screen updates back in the other direction, over a network.
About this security research
As security researchers we going to search for open VNC ports to detect misconfigured and vulnerable systems with help of Shodan search. After such systems will be detected our main aim will be to alert owners of the targeted systems.
Such way we will train our skill to execute search through shodan and help technical owners to help their systems.
Detecting vulnerable & misconfigured VNC systems
On the first step you need to open shodan and go to the search page. Than we need to start search for VNC with open access.
Default VNC ports are 5901, 5900 and 5800 so we will need to search for them and we can as well make limits by country or region for example.
Our query will be like:
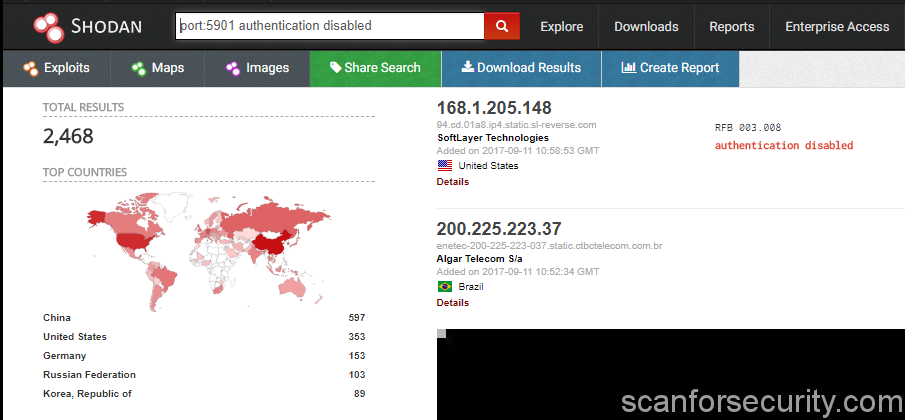
port:5901 authentication disabled
For all available systems with open VNC ports all over the world.
Or we can limit for exmaple by US:
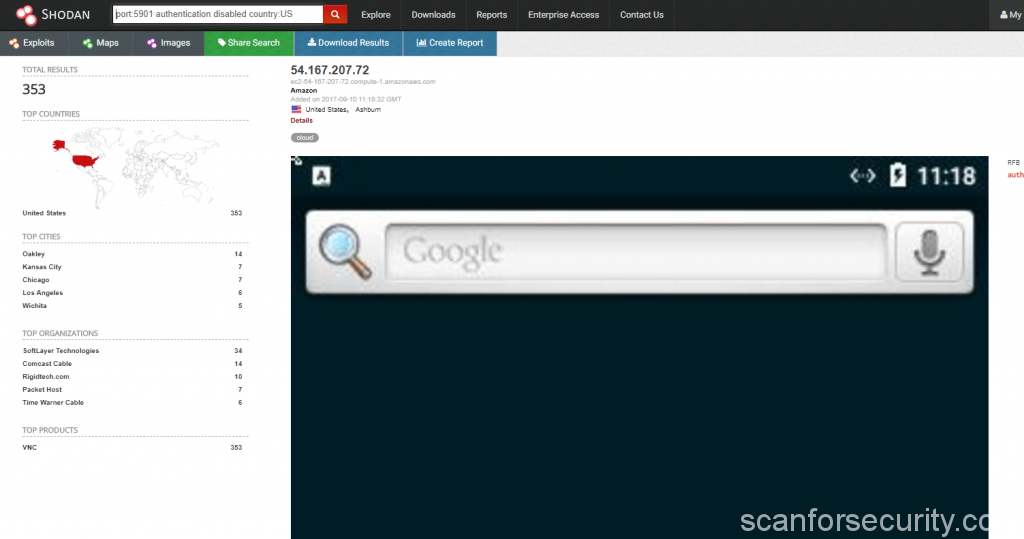
port:5901 authentication disabled country:US
“Authentication disabled” means that VNC service working on the specific port 5901 will be available without any kind of authentication, you can login and watch what happens on the screen.
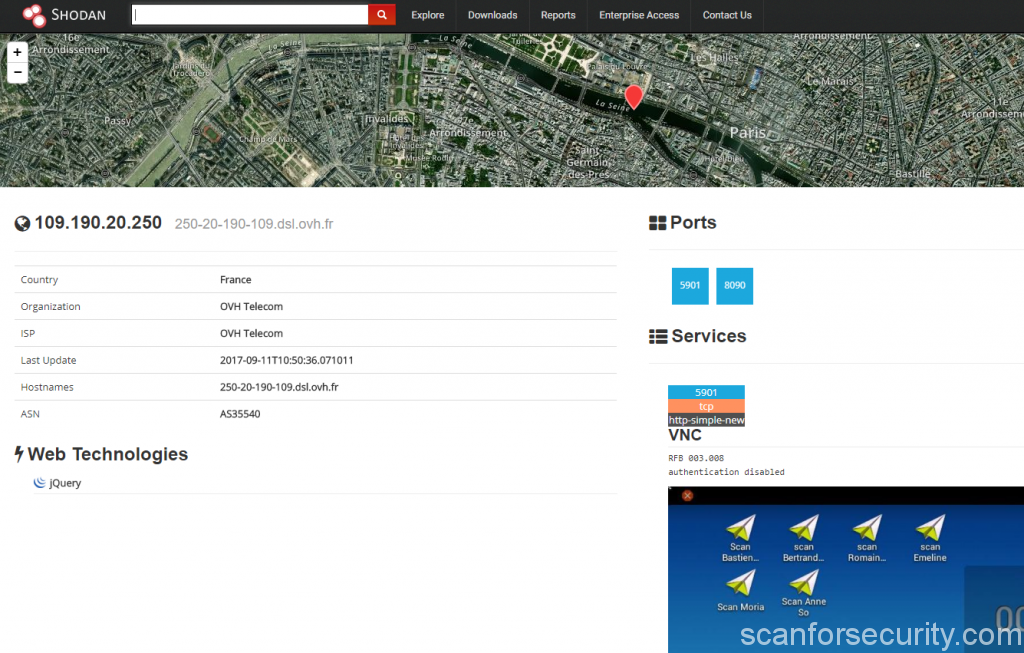
After you will receive shodan search results, just click on any of them and you will see other details about the system:
From what we can see, there are over 2.000 systems with open VNC service available all over the world. You can try to connect to any of them but remeber, that you will violate the law with such kind of actions.
Best thing you can do – report to the system owner about the issue and wait for the resposne.


























Is there a means of detecting VNC if the user’s been smart and moved it away from the default ports?
It is possible to identify VNC also by banner grabbing. So if we speak about common bot scans – it gives them less chance to guess VNC service running, but if it will be real pentester for example, he will find VNC on another random port without any problems. The only solution – limit access on port with help of firewall rules.
Comments are closed.