What is GDPR?
The General Data Protection Regulation (GDPR) is focused on the personal data of citizens within the European Union. GDPR is often viewed as having two primary goals within the EU and beyond;
- To define the online rights of EU citizens.
- To regulate the handling of EU citizen’s personal data.
A key goal of GDPR is to provide EU citizens with more control over their own data. You’ve probably noticed the ads of products online after searching for that same product just a day prior. It’s no coincidence, but instead because of data collected the day prior. GDPR sets out to make this optional & completely up to the individual. Under GDPR, individuals have a handful of rights:
- To be informed: Before data is collected on individuals, the individual must knowingly give consent.
- Access: If requested, companies must provide individuals access to what data has been collected about them and how that data is being used.
- Rectification: If data is old or incorrect, individuals have the right to have the data corrected.
- Erasure: If an individual is no longer a customer, or has withdrawn approval of data collection, then an individual has the right to have data fully deleted.
- To Restrict Processing: An individual has the right to request their data not be used for any processing, but the data does not have to be deleted.
- Data Portability: An individual has the right to have data moved from one company to another.
- To Object: Individuals have the right to immediately stop their data from being used in direct marketing.
- Rights related to automated decision making including profiling: Individuals have the right to know if automated decision making is being used in a way that can impact them.
In addition to individual rights, GDPR also aims to regulate how personal data such as name, email, address, ect is handled. Companies must be transparent in what information is collected and how it will be used. As you may have noticed by the multiple privacy policy updates you’ve received; Companies are not only explaining how data is captured, stored, and used, but also secured. While GDPR is primarily viewed as a privacy standard, there are also underlying roots in security.
GDPR Penetration Testing
Do you need a penetration test for the GDPR?
The GDPR recommends that you assess applications and critical infrastructure for security vulnerabilities and that the effectiveness of your security controls are tested regularly, services such as penetration testing and regular vulnerability assessments would help meet this recommendation. And with breach reports being legally required (no later than 72 hours) can you afford not to have a penetration test performed.
At first glance GDPR may seem as if it doesn’t have much to do with penetration testing. With some fine reading, you can find a direct correlation under Article 32;
“(d) a process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures for ensuring the security of the processing.
This is vague as it doesn’t specifically define what must be tested on a regular basis. A strong rule of thumb is that any systems or applications that touch personal data. If Article 32 isn’t enough of a reason to understand why penetration testing is an important security factor of GDPR, the mandatory breach disclosure should be enough of an incentive. The days of delaying breach disclosures are over as you must now announce an incident within 72 hours of the discovery. Penetration tests can discover vulnerabilities or potential breaches before anyone else, ultimately saving you the pain of breach disclosure.
GDPR will create the perfect reason to have regular penetration tests, but when it comes down to it penetration tests are helpful to any team. Most security professionals can relate to the full plate that others in the industry have. Beyond just identifying vulnerabilities prior to real-world exploitation, penetration tests help teams prioritize security fixes based on the severity and impact of different findings.
Aside from any specific requirements, GDPR has harsh penalties for a security breach, with organizations facing penalties of up to 20 million euros, or 4 percent of worldwide annual turnover, whichever is higher. With financial impacts so hefty, thorough proactive controls are critical.
Penetration tests are crucial because they provide a final, end-of-state check to make sure all the security controls required have been implemented correctly. They can also be used in the early stages of developing new processing systems to identify risks to personal data.
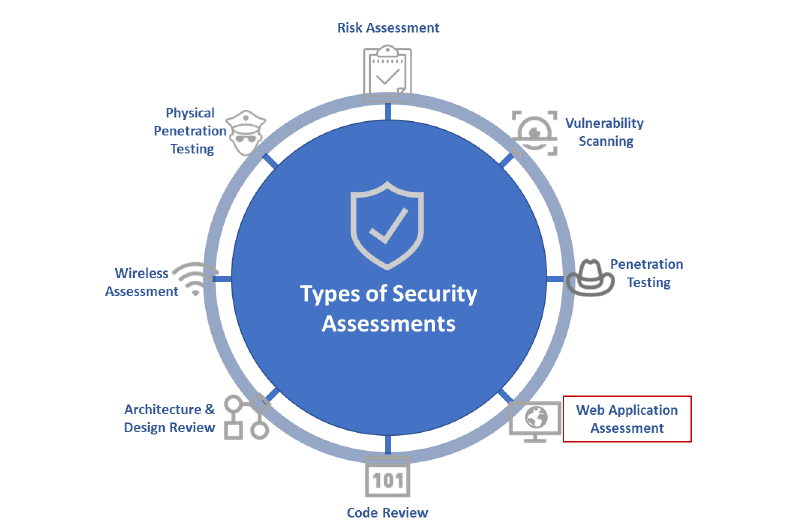
What other security assessments are recommended for GDPR?
In order to fulfill the requirements prescribed by GDPR, you have to focus on various areas inside your organization while conducting a vulnerability assessment and penetration testing activity.
- Critical Systems: To start with, you must identify critical systems or processes which are integral for your business operations as well as meeting with the compliance requirements. For GDPR, critical systems will involve the systems processing as well as securing personal data of EU residents.
- Social Engineering: If something is said to be with assurance, then humans are the weakest links in the entire cybersecurity ecosystem. According to various reports published by the industry leaders, the majority of malware, for example, ransomware, are installed and executed on victim systems via email attachments. One of the most cost-effective methods is to train employees by making them experience a real-life social engineering attack, but this method is either not used at all or often unused. Conducting a simulated real-life attack can help an organization in quickly identifying the issue – if its an internal awareness problem or a group of employees who require extra hands-on training. While planning a simulated attack, you must consider the size, complexity, and awareness maturity of your organization.
- Network Layer: There are two sides to network testing – external and internal. Externally, how the organizational network gets connected to the internet must be checked. While internally, how does it protect itself from internal threats must be examined. An organization must not solely rely on automated tools, manual testing procedures must be performed alongside automated testing. Advanced testing can involve attempts to bypass authentication control to penetrate into the organization’s network. On a broader level, an organization should make sure that it –
- Assesses all the vulnerabilities that could be exploited by an attacker
- Verifies that the services which are authorized explicitly are exposed to the data environment
- Application Layer: Apart from the vulnerabilities that are found in enterprise applications, web-based applications are prone to attacks such as XSS, SQL injection, etc. Here, the testing should focus on addressing the risk of such attacks so that potential attack vectors can be minimized.
- Network Segmentation: Properly segmenting networks is a simple yet effective way to significantly reduce risks and damages in case of a data breach by isolating the infected segment. After an organizational network has been segmented, appropriate tests must be conducted to ensure that controls are in place and they are effective.
Conclusion
As we see from the above, specifically for the GDPR, there is no particular type of penetration testing approach, there are, perhaps, some points that should be paid more attention to. The main message is that the penetration testing itself is one of the processes of compliance with the GDPR policy, but as such a penetration testing is just a small part of the overall process.
To properly protect your personal users data better to execute two types of checks – internal (audit) and external (pentesting), as well as use proven cloud platforms (i.e.: AWS by default complies with the requirements of the GDPR).