Vega is a free and open source web security scanner and web security testing platform to test the security of web applications. Vega can help you find and validate SQL Injection, Cross-Site Scripting (XSS), inadvertently disclosed sensitive information, and other vulnerabilities. It is written in Java, GUI based, and runs on Linux, OS X, and Windows.
Vega can help you find vulnerabilities such as: reflected cross-site scripting, stored cross-site scripting, blind SQL injection, remote file include, shell injection, and others. Vega also probes for TLS / SSL security settings and identifies opportunities for improving the security of your TLS servers.
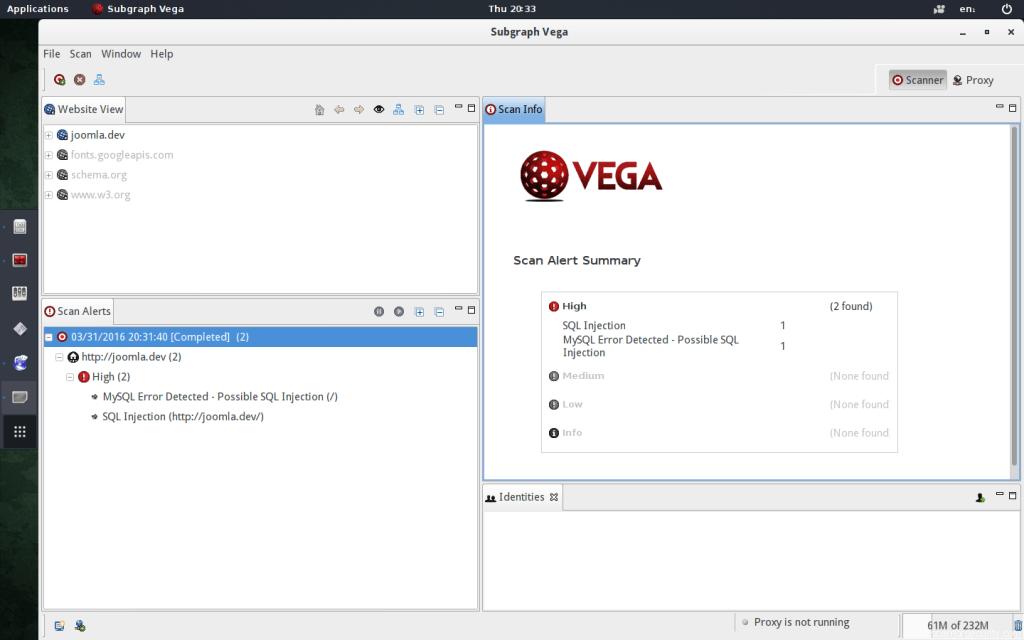
Vega includes an automated scanner for quick tests and an intercepting proxy for tactical inspection. The Vega scanner finds XSS (cross-site scripting), SQL injection, and other vulnerabilities. Vega can be extended using a powerful API in the language of the web: Javascript.
How does Vega work?
Vega includes an automated scanner for quick tests and an intercepting proxy for tactical inspection. The Vega scanner finds XSS (cross-site scripting), SQL injection, and other vulnerabilities. It can be extended using a powerful API in the language of the web: Javascript.
Vega Features:
- GUI Based
Vega has a well-designed graphical user-interface. - Multi-platform
Vega is written in Java and runs on Linux, OS X, and Windows. - Extensible
Vega detection modules are written in Javascript. It is easy to create new attack modules using the rich API exposed by Vega.
Scanning with Vega
To start a scan that will crawl the entire site and only check for XSS:
- Click scan > ‘start new scan’ .
- In the dialog that appears, enter your target websites url as the ‘base’
- Click next.
To scan a single page only:
- Click ‘Choose a Target Scope’.
- Then Click ‘Edit Scopes’.
- Next, either add a new scope, or edit an existing one.
- Add each url to the scope.
- Click ‘OK’.
By default vega vulnerability scanner will scan for lots of different vulnerability types.
- Header Injections.
- Directory Traversal Attacks.
- URL Injection Attacks.
- XML Injection Attacks.
- XSS Injections.
- Blind SQL Injections.
- Shell Injection Attacks.
- Remote file include Attacks.
- String Format attacks.
- OS Command Injection Attacks.
You can download Vega from official website by this link.
Here you can find additional Vega web application security scanner wiki.






















